Disruption is the most significant trend we have seen this year. The global pandemic brought disruption encompassing all things familiar and dear to us. It upended the way we live, work, and interact with the world around us.
Touchless solutions came to the forefront as social distancing measures were strictly put in place. Businesses big and small alike had to quickly adjust and move their businesses online or remotely in this new normal economy.
What was alarming, but not at all surprising, was the increase of cybersecurity threats in 2020. Cybercriminals were exploiting wherever they could, from hospital databases to financial records, ransomware, phishing emails, and the like.
Cybersecurity for businesses had to step up to the new waves of attacks, and so did business networks and databases. As the pandemic fuels cyber-attacks, it is exposing gaps and vulnerabilities in business recovery.
Around 91% of businesses state that they experienced increased attacks, especially since employees had to work from home and use their own devices.
Microsoft also estimates phishing and social engineering attacks related to Covid-19 have grown to around 30,000 a day in the U.S. alone. MonsterCloud security analysts also say that ransomware attacks increased to a staggering 800% since the pandemic.
It is why we need heightened security awareness more than ever. See this list below of upcoming trends and threats to cybersecurity this 2023.
Top 5 Cybersecurity Threats to Avoid in 2023
1. Remote workers will be the target of cybercriminals throughout 2023.

Remote workers, whether they work from their homes or co-working spaces and the like, will continue to be attacked by hackers this 2023. Cyber attackers look for vulnerabilities they can exploit to attack both the remote worker and the company that they work for.
Unsecured connections are among the top vulnerabilities, which often happens in a BYOD system (Bring Your Own Device). Remote workers usually tap into networks not protected by their company, like public access wifi in cafes or restaurants.
Remote workers, and any other employee for that matter, can also succumb to phishing emails or text messages. When hackers are successful in illegally tapping into a remote worker’s device, it is easier for them to tap into the company’s system through access credentials in that person’s device.
And no matter how much companies try to build security awareness among their teams, it does not make their team immune to attacks. In fact, ransomware attackers specifically target CEOs and other top-tiered employees to make their ransom attacks more profitable and worthwhile.
So, in 2023, experts agree that cyber attackers will still track users and initiate attacks that abuse their behavior to threaten businesses’ defense postures, as many are still unable to support a remote workforce safely.
Businesses need to tighten their grip on their remote team’s security. Investments to fix cybersecurity breaches and infections and to harden defense systems are required.
If companies do not improve their compliance approaches, cybercrime will continue to grow. Hackers will also continue to manipulate remote employees as perfect entry points into corporate IT environments.
2. Fileless Attacks

According to leading cybersecurity company McAfee, fileless malware is malicious software using legitimate apps or programs to infect a user’s computer. It is not file-reliant and leaves no footprint. It is why it is challenging to detect and to remove.
It is especially so because attackers usually are already familiar with how organizations will try to block their attacks. Attackers study the defense systems of organizations they target, so their attacks are successful. Hackers are creating increasingly elaborate and highly targeted malware to deflect the security defenses of their target.
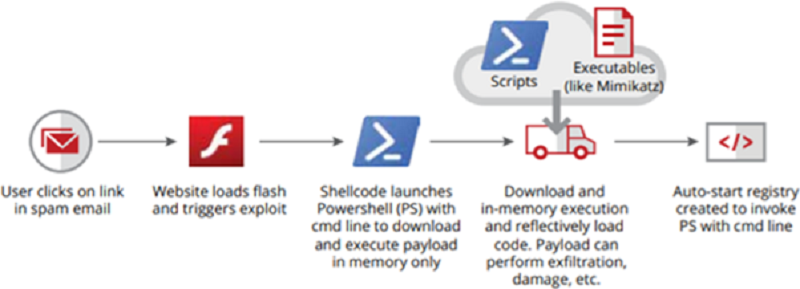
The most effective hacking strategies are the newest ones because security systems are not prepared for them yet. Fileless malware attacks have been deadly this way, effectively avoiding the most robust security solutions.
It is why having top-of-the-line, reliable, robust, and total security protection is a must.
3. Compromised Business Process Attacks

Cybercriminals often find flaws, not in software but the business process flow. We see a spike in business intelligence compromises in which attackers leverage structural, institutional loopholes for their malicious gain.
Attacks in business processes often start with a compromised network infrastructure. From there, cybercriminals monitor how these businesses operate, including their defense systems, so that they can find weak links.
However, these attacks are very covert, so organizations affected cannot even identify them promptly, especially when the compromised mechanism appears to function ‘as planned.’
For instance, attackers can siphon funds by compromising electronic invoicing software and modifying bank account numbers that are populated into any potential invoice.
4. Customized Payloads

Targeted attacks may take extra work on the part of attackers, but they are far more effective in breaching networks and records. It is why cybercriminals do these kinds of attacks heavily, and the attacks are becoming more and more sophisticated.
Cyber attackers study a network’s business blogs, social media, and other public accounts. They will also use data they have gathered from breaching individual network systems.
Pervasive and dual-use applications like PowerShell and WMI allow attackers to discover more about the company’s tools and resources without setting red flags. Armed with these techniques and their vulnerabilities, cyber attackers create payloads specially designed to bring down networks.
Malicious payloads harm their victims through the following:
- Data theft/data breaches.
- Activity Monitoring, blackmailing, spying
- Displaying advertisements
- Deleting or modifying files
- Downloading new files with a malicious virus.
- Running background processes
To prevent malicious payload attacks, you need to layer up on security measures. Businesses need to set up more secure access management systems, standardizing the use of VPN (Virtual Private Network) for all their employees, aside from the usual cybersecurity software installed on devices and networks to prevent a data breach, virus attacks, and malware attacks.
5. Accelerating Ransomware Attacks
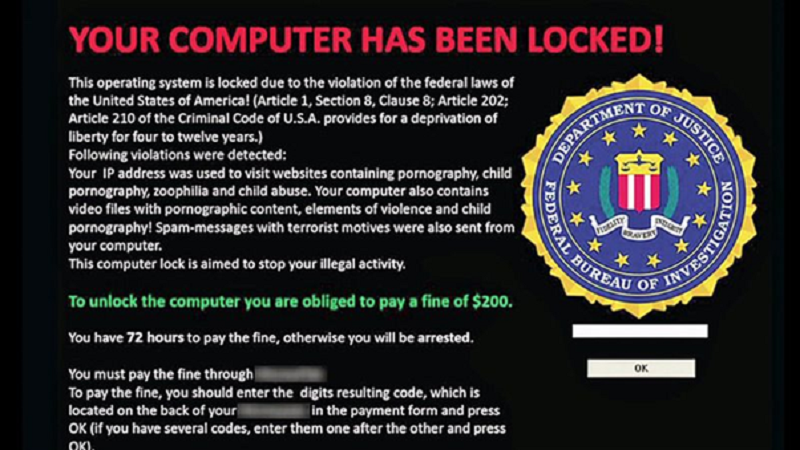
commons.wikimedia.org
Cybersecurity Projects has crunched historical figures in cybercrime, forecasting a company could fall prey to a malware attack every 11 seconds in 2023. That is down every 14 seconds in 2019.
Ransomware’s overall damage would surpass $20 billion worldwide. That said, any company must employ simple cybersecurity. As easy as installing antiviruses on treated group and smartphones will deter security attacks like ransomware.
Invest in reputable and checked antivirus applications to ensure the device blocks attacks. Cybercriminals are getting smarter. When they get into a device, they will crawl their attack through the network.
Top 5 Trends to Watch Out for in 2023
1. Enhanced Cloud Security Monitoring
There will be increased adoption of cloud technology, especially in response to stay-at-home necessities. Businesses are currently taking a more proactive stance on improving their cloud protection systems.
Organizations planning to develop their digital presence further will concentrate on cloud-based applications that help them identify and fix misconfigurations faster.
2. Location-Agnostic Operations
Businesses can build location-agnostic operations to serve clients anywhere and allow staff to work remotely and handle business services through global networks.
This operating model enables corporate access, delivery, and control anywhere—where customers, employers, and business associates work in remote locations. Businesses need to invest in technology infrastructure, new management strategies, and resilient compliance and governance frameworks to offer unique, seamless, and scalable digital experiences.
3. Responsible AI
Artificial Intelligence (AI) is an increasingly advancing technology that powers many modern-day touchless solutions, including machine learning scalability, advances.
However, there is a growing concern regarding its disruptive effects, like labor disruption, privacy loss, possible prejudices in decision-making, and loss of responsibility for automated processes and robotics.
Responsible AI will be increasingly in demand. It ensures that the ethical, open, and accountable application of AI technology is consistent with consumer preferences, corporate principles, and community laws and standards.
4. Increased adoption of proactive cybersecurity solutions
As businesses continue to avoid physical health problems for employees preemptively, they must also prevent cybersecurity threats associated with each of these improvements.
AI (artificial intelligence) and Machine Learning applications with rich data sets ensure companies evaluate hazard trends correctly, eventually keeping track of emerging methodologies.
The 2020 IBM Cost of a Data Breach study confirms the benefits of these solutions on cybersecurity. AI and ML decreased the total data breach cost by $259,354.
5. Endpoint Management
Remote workforce and distributed devices requesting access to the company assets require robust security and access management. An organization’s ability to centrally discover, supply, deploy, update, and manually configure endpoint devices must be hardened.
Managing endpoints is critical, as these endpoints can be the point of entry for corporate cybercrime networks.
Using an endpoint management system provides companies with several advantages: securing remote workers, handling endpoint conditions, automating procurement and enforcement, and enabling streamlined endpoint troubleshooting.
Conclusion: Harden Your Business Security for 2023

Businesses and enterprises must change their cybersecurity and data security strategies to adapt to the new trends and threats in cybersecurity. If cyber attackers continue to adjust their technology and attack methods, how much more should businesses’ defense systems be hardened against emerging threats?
Businesses need to secure all their workloads, data, and applications across all platforms they use. They need to set-up automated frameworks to simplify device management, risk evaluations, and endpoint security. In this manner, they will be more equipped to stop emerging threats in real-time.

Mayleen Meñez used to work in media before finding her true passion in NGO work, travelling the Philippines and Asia doing so. She homeschools 3 kids and loves reinventing Filipino dishes. She is a resident SEO writer for Softvire Australia and Softvire New Zealand.
Mayleen Meñez Social Credentials
Facebook: https://www.facebook.com/mayleenmenez
Twitter: https://twitter.com/MayleenMenez
LinkedIN: https://www.linkedin.com/in/mayleenmenez/
Instagram: https://www.instagram.com/mayleen_menez/


