History hiding is a common issue nowadays. I think everyone has a few things in their browser history that they might be ashamed of. It’s common enough to be a running joke along the lines of, “Delete my browser history when I die.”
Periodically clearing out your browser history is like taking out the trash: It has to be done or things just heap up (and it can slow your computer down). People also tend to be just as ashamed of their browsing history as they are of their trash bags.
Deleting your browser history is pretty normal.
But sometimes deleting history can be done with nefarious intent, too.
When Deleting Browser History Becomes Suspicious
People who access pirated or pornographic content from their school or office computers might delete their history the moment they’ve done it.
The same is true for people who are cheating on their partners, people who might be siphoning information or money from their employers – or people who are accessing illegal content of any kind.
If you suspect that a system under your control is used by an illegal history hider who is accessing things they shouldn’t be, there are a few ways to check – and in some cases, what you find should be reported to law enforcement if it involves any illegal activity.
Here’s how to catch a history hider if you are a system administrator, librarian, internet cafe owner, concerned partner or employer.
Is Looking Illegal
Are you allowed to look at someone’s internet history? The first step is to establish what the legal answer is.
In most cases, if you are the system administrator, the owner or an employer, you’re allowed to look at the internet history for any systems that are under your control – but if you don’t own the PC or network, it becomes a gray area where it might be best to call a professional such as a private investigator to take over the search.
Don’t opt for keyloggers: These can sometimes get you in more legal trouble than they are worth, and many keyloggers are spyware in disguise.
1. You’re On Camera

If you aren’t sure what someone has been accessing and you begin to suspect it blurs the line towards illegal, many employers will have CCTV-systems where the screen of a computer is clearly visible.
If you suspect an employee is playing Solitaire or watching pornography, start by checking the camera footage.
2. Searches While Logged In
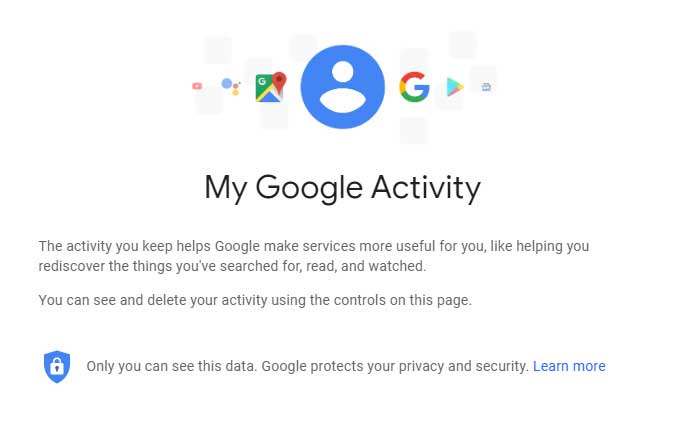
If someone has remained logged into their social media accounts (such as Google) while doing searching, clearing the browser history won’t clear the online Google search history.
It usually appears under Google’s My Activity page. Any searches that were made while logged in will appear here.
3. Gaps In The Browser History
Does it look like someone hasn’t accessed any links for a four-hour time period while the rest of their history is filled up? That means you have a gap – and unless they’re a time traveler or they were truly offline for this period of time, they’ve been selectively masking their search history.
It’s likely that the person in question either deletes the pages they have been visiting from the browser history or switches over to the browser’s Incognito Mode to access whatever they’re opening up.
4. Recovering Browser History
Sure, you can clear your browser history as much as you want, but even if you poured acid on your hard drive and run it over with a train the history would still be backed up in several different places (and probably recoverable from the hard drive itself!).
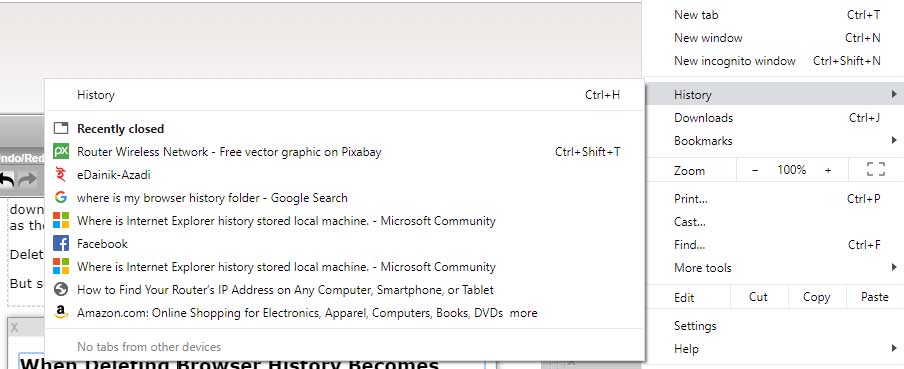
Powerful file recovery programs can sometimes help to restore the files that are found in the browser history folders. It’s different for each browser, so just type “Where is my browser history folder?” into the search engine to find the appropriate folder you’ll need to recover things from.
This is usually a valid solution for Linux, Windows and Android systems.
Visit the folder to see what was accessed.
5. The Router IP

Internet routers record everything.
This means that internet routers will generally store every single site that was accessed in its own history even if the computer or browser’s history was destroyed.
If you open up your browser and type the internet router’s IP address in the web address bar, this takes you to the internet router’s login page. Usually, it’s set to a default password and you’ll have to check the manual for the applicable router to find out what this is.
See this page on how to find the IP address for your router or Android device.
All the accessed sites, whether deleted from the browser history, will show up here.
6. Other Attempts To Hide
There are many other methods people might use in an attempt to hide their tracks. Here are a few of these that might tip you off that an internet user is up to something they shouldn’t be.
- The Use of Certain Search Engines
Search engines like DuckDuckGo are often used by people who want to be more internet secure. But if sites like these keep showing up in the history, you might be able to conclude that someone is trying to hide their searches in one form or another.
- Duplicate Social Media Accounts
Duplicate social media accounts with either the same images or the same name (and in some cases, neither of these but accessed by the same person) can be a tip-off that someone is attempting to hide behavior from their main social media account. Sometimes it’s to separate professional and business – but other times, it could be for more sinister things. - Dark Web Access
A lot of curious internet users access what’s called the dark web out of curiosity once, but repeated access to it is unlikely to be a good thing – and unlikely to be for anything legal. Using dark web-specific browsers like Tor can be a sign that someone has been digging in the dark.
The Last Step
What to do next depends on what you’ve found.
Content that isn’t of a legal nature such as wasting time on Solitaire while they should have been at work or infidelities online should be handled at your own discretion.
Any illegal content, especially pornography of an illegal type, should be immediately reported to the authorities. This means stop what you’re doing, don’t be a hero, never try to confront the person in question and go straight to law enforcement. Any evidence that you are aware of should be handed over for an investigation to be opened.
Any illegal gambling activities should be reported to the relevant regulatory board first and usually the authorities second.


