
A wi-fi connection is how most individuals and companies find their way to the internet. But how many of these realize just how vulnerable wi-fi has the potential to be – and is yours protected enough right now?
The average hacker looks for any available vulnerability within a probed system. Most wi-fi connections are not completely watertight: Comcast reports estimate that the average smart home might see as many as 104 attempted hacks per month which could go unnoticed by the user.
Public wi-fi use is notorious for being unsafe for transferring personal or secure information. Unfortunately, home, and corporate wi-fi connections are not much safer and are especially vulnerable to even the novice coder with malicious intent.
As more individuals spend time at home for business, reports indicate that hacking attempts aimed at home wi-fi connections (and smart devices) might be well on the rise.
If you are worried about the security of your home’s internet connection, you should be.
Here are 7 scary things hackers can do with your wi-fi connection (and any devices linked to it).
1. The Ghost in The Coffee Maker
Smart coffee makers are meant for the average person who really loves their coffee, but many might also be in offices where one of the most popular beverages gets enjoyed.
A penetration tester decided to test how easily smart coffee makers are to crack and came up with a terrifying scenario.
Using the coffee maker’s connection, several of the most essential functions could be altered to the fullest. The machine could be set to start at random intervals or spray the user with warm water going far above the allowed temperature.
Did you ever imagine a time when coffee makers could be hacked to turn on its user?
The time is now.
2. Smart Plugs

Smart plugs are a common sight within the modern home.
The average smart plug gives users the ability to monitor every connected power source and control it via the use of an included app or software.
Unfortunately for most users, connected plugs have been shown to be just as vulnerable to the hack as any other internet-linked item out there.
With some skills and creativity, a hacker might have the ability to control and monitor the same devices which the administrating user can. With more malicious intentions, a hacker can reportedly even trigger a fire through a smart plug-hack.
Do smart homes still seem like a great idea for the future?
3. Surveillance Companies
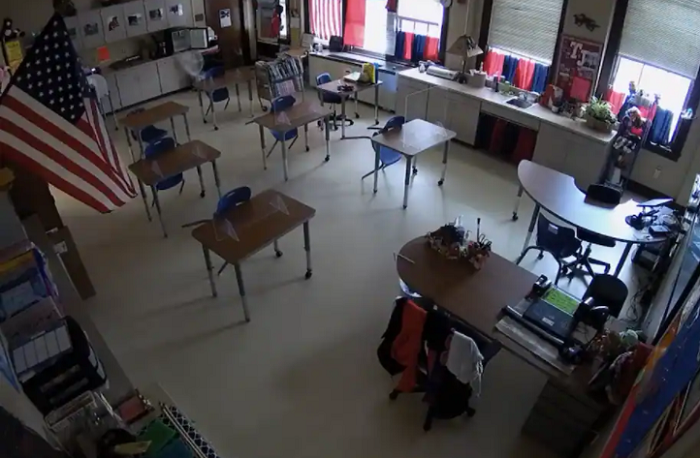
Cybersecurity and surveillance companies are not immune to being compromised, as one of the most widely reported security breaches of 2021 will show.
Verkada, a high-profile surveillance provider that calls itself an “enterprise security camera system”, found their systems infiltrated – and all their surveillance feeds laid bare for prying eyes to watch.
When a security or surveillance company gets hacked, it is a risk for all their connected clients. Always take note of who your security provider is (and when events like this take place).
4. Doorbell

The smart doorbell is meant to put homeowners at ease, with a video feed linking straight to their front door to let them know when anyone might show up.
In 2020, the true vulnerability potential of smart doorbell systems became clear when hackers penetrated video feeds across the world with more ease than one would imagine.
Access to the smart doorbell grants a potential criminal the ability to view everything the user might.
Would you feel safe knowing that someone else might be hacked into your home’s video feed?
No user would, and Amazon is facing the potential of lawsuits from Amazon Ring users who were hacked.
5. Google Nest

Google Nest is an attempt to make the concept of the smart-home far more commonplace, and thousands of users have already considered the switch.
The Nest is a virtual assistant that links users up to their house with instant control. Functions within a Nest-controlled home can be monitored or changed in an instant, with the option of voice recognition.
Security and safety are certainly two of the primary selling points for Google’s intelligent house assistant. But how easy is the system to penetrate?
In a horrifying tale that seems like it should be straight from fiction, a couple was targeted through access to their Google Nest device. From there, hackers pushed the couple to their limits by using their devices to threaten them right in their home.
What if your dream smart-home became a nightmare?
6. Smart Baby Monitors

Parents and couples rely on the reassurance of baby monitors to keep a watchful, remote eye on their child and surroundings. But should they?
Smart baby monitors can be hacked, according to both cybersecurity experts and existing victims of the hack.
Due to the smart monitor’s ability to connect to the internet, it can be just as easy to hack as a coffee maker or doorbell.
In an instant, hackers can view your entire home with as much capacity as they would like – or keep a closer eye on your children than you would want anyone to have.
7. Apple Wireless

Apple Wireless might be one of the largest tech megaliths of the modern age, but this does not guarantee that their systems are impenetrable.
In a 2020 attack reported by BBC News, hackers found a vulnerability within the Apple Wireless Direct Link wi-fi connection that allows complete, remote access to the device itself.
Even without describing the event without any technological jargon, most can tell exactly how much of a security risk this might present to their own, personal devices.
How confident are you in the security of your device?
Always backup (and update).
If you want to know more about finding the best cybersecurity software you can read our article on the subject by clicking here.
This is a guest post contribution from Alex J Coyne
Editor’s Note
Alex writes excellent cybersecurity guest post articles for us and it is looking for paid work in that field. If you are looking for a top cybersecurity writer, send us an email at john@identity-theft-scout.com and we will put you in touch with him.


